Every healthcare organization needs to understand HIPAA requirements. More than that, you need to implement policies and procedures to ensure compliance — including training your staff on HIPAA regulations, implementing technical safeguards for protected health information (PHI), and providing proper documentation and reporting of potential breaches.
Compliance with HIPAA standards demonstrates your commitment to protecting patient privacy and security, and helps ensure your organization avoids legal and financial consequences for non-compliance.
Expansion and Changes to HIPAA Rules
Since its enactment in 1996, HIPAA has gone through some changes to become the robust healthcare privacy standard we use today. When HIPAA and other healthcare-related laws and regulations receive updates, providers and staff must educate themselves on these updates to remain compliant and, in turn, keep their facility compliant.
There have been many healthcare privacy laws passed in modern history:
- 1996: U.S. Congress enacts HIPAA to establish national standards for protecting the privacy and security of individuals’ health information.
- 2009: The Health Information Technology for Economic and Clinical Health (HITECH) Act is part of the American Recovery and Reinvestment Act (ARRA) of 2009. HITECH includes provisions to promote healthcare providers’ adoption and meaningful use of electronic health records (EHRs).
- 2010: The Centers for Medicare and Medicaid Services (CMS) implement the Medicare and Medicaid EHR Incentive Programs to provide financial incentives to eligible healthcare providers who adopt and demonstrate meaningful use of certified EHR technology.
- 2013: The HIPAA Omnibus Rule modifies and strengthens HIPAA regulations, including expanding the definition of a breach and implementing stricter provider requirements.
- 2015: The Medicare Access and CHIP Reauthorization Act (MACRA) features the Merit-based Incentive Payment System (MIPS), consolidating various quality reporting programs, including EHR Incentive Programs.
- 2016: The 21st Century Cures Act contains provisions to promote the adoption of EHRs and the interoperability of health information technology.
As technology evolves, healthcare providers must stay current on the latest law changes to ensure they provide high-quality care and protect individuals’ health information.
Overview of HIPAA Compliance
Since its enactment, HIPAA rules have been expanded and amended due to new laws and regulations. These changes affect existing privacy, security, and breach notification requirements and have resulted in stricter enforcement of HIPAA rules by the Department of Health and Human Services (HHS).
Three Core Compliance Elements of HIPAA
By breaking up the core compliance elements into three silos, HIPAA provides a comprehensive framework for protecting individuals’ health information throughout its life cycle, from collection to disposal. It ensures that providers have the necessary tools and requirements to safeguard patient information’s confidentiality, integrity, and availability.
1. Privacy Rule
It restricts the use and disclosure of an individual’s PHI without authorization. The rule also allows the disclosure of PHI necessary for patient care and other purposes, such as public health activities or law enforcement. The Privacy Rule defines PHI as individually identifiable health information that is held or transmitted in any form or medium, whether electronic, paper, or oral.
2. Security Rule
This rule requires owners and providers to implement administrative, physical, and technical safeguards to protect the confidentiality, integrity, and availability of electronic PHI (ePHI). Staff must perform regular risk assessments to identify potential vulnerabilities and implement reasonable and appropriate measures to mitigate those risks.
3. Breach Notification Rule
Facilities must notify affected individuals, HHS, and sometimes the media in case of a breach of unsecured PHI. A breach is the acquisition, access, use, or disclosure of PHI in a manner not permitted by the Privacy Rule, which compromises the security or privacy of the PHI. Facility owners must provide notification within 60 days of the breach’s discovery.
Creating a Compliance Plan
To comply with HIPAA regulations, healthcare facilities and their staff must have a formal and organized compliance plan that should include the following:
- Policies and procedures related to HIPAA regulations
- Training for all staff members on HIPAA compliance
- Regular reviews and updates to ensure ongoing compliance
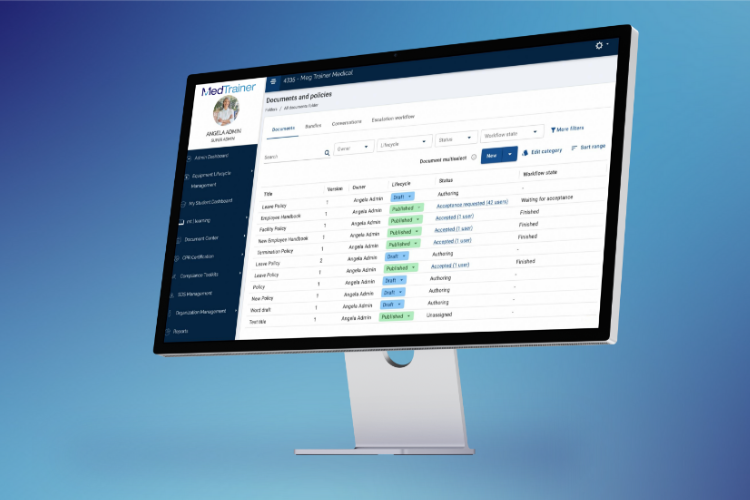
Streamline your compliance with MedTrainer
Consequences of HIPAA Non-Compliance
The consequences of not complying with HIPAA standards can be significant. Providers can be subject to audits and investigations by the Office for Civil Rights (OCR), which can result in penalties, fines, and reputational damage from $100 to $50,000 per violation, depending on the severity of the violation, up to a maximum of $1.5 million per year. Following a formal and organized compliance plan can help facilities and their providers avoid these consequences and improve patient care.
HIPAA Compliance Training
If you handle PHI, you need to receive education on HIPAA. Compliance training on HIPAA typically involves completing a series of courses that provide education on the various aspects of HIPAA regulations, ensuring that all personnel handling PHI know their responsibilities and how to maintain compliance with HIPAA.
MedTrainer offers HIPAA courses and other healthcare compliance training options. Training occurs through our online platform, which offers a variety of courses and educational materials, including webinars, videos, quizzes, and other resources.
The steps to completing HIPAA training may vary depending on the provider but generally involve the following:
- Register for the training program
- Complete the required courses and educational materials
- Pass any required quizzes or assessments to demonstrate knowledge of the material
- Receive a certificate of completion or other documentation
Refresher courses are necessary, as HIPAA regulations may change over time. It is important for healthcare providers and their staff to stay up-to-date with the latest regulations and compliance requirements to ensure that they are protecting individuals’ health information and maintaining compliance with HIPAA.
Now’s the Time to Focus On HIPAA Compliance Training
HIPAA compliance is a critical requirement for all facilities and their providers in the healthcare industry. The implementation of national standards for all electronic healthcare transactions and the increase in electronic data interchange usage have made compliance education and the creation of a formal HIPAA compliance plan more important than ever.
Failure to comply with HIPAA regulations can result in severe consequences, including fines, penalties, and reputational damage.
MedTrainer offers a solution to this challenge. We provide HIPAA compliance training to help facilities and their providers stay up-to-date with the latest HIPAA regulations and ensure their staff is knowledgeable in HIPAA’s Administrative Simplification provisions, Privacy, Security, and Breach Notification requirements, and the other core compliance areas of HIPAA.
MedTrainer provides the education and training necessary to create a formal and organized compliance plan. We help facilities and their providers avoid potential penalties and reputational damage. Contact us today to learn more about our compliance services.